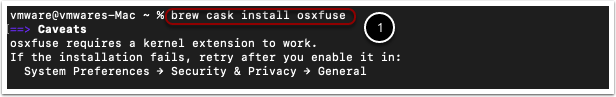
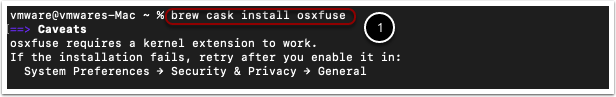
Homebrew Docker Virtualbox (But not only VirtualBox) This formula resolves the Docker issue on AMD based MacOS (Ryzentosh). Also can be used on any Mac. Like the caveat notes when brew finishes, you need to update the launchd plist for ssh-agent to use the new Homebrew binary. By replacing /usr/bin/ssh-agent with /usr/local/bin/ssh-agent $ launchctl stop org.openbsd.ssh-agent $ launchctl unload -w /System/Library/LaunchAgents/org.openbsd.ssh-agent.plist. If you have MacOS there’s a chance you don’t have ssh-copy-id installed, in that case you can install it using brew install ssh-copy-id. The file that has no extension is your private key. Brew tap by default clones via HTTPS, not SSH. You will need to use the two-argument form to specify the e.g., git@github.com. See brew tap -help for details. I mentioned already that cloning any http repo works fine. So, I dunno why is brew tap asking for my credentials?

$ brew install composer # SSH keys # Create SSH key. Trellis and GitHub both use SSH keys to communicate securely without the need to type a username and password.
- PDF Link: cheatsheet-ssh-A4.pdf, Category: tools
- Blog URL: https://cheatsheet.dennyzhang.com/cheatsheet-ssh-A4
- Related posts: Tmux/Tmate Cheatsheet, #denny-cheatsheets
File me Issues or star this repo.
1.1 SSH general
| Name | Summary |
|---|
| ssh without input password | sshpass -p '<your-passwd>' ssh <username>@<ssh_host>, brew install sshpass |
| Install sshd server | apt-get install openssh, apt-get install openssh-server |
| Restart sshd server | service sshd restart, systemctl reload sshd.service |
| Run ssh command | ssh -o StrictHostKeyChecking=no -p 2702 root@172.17.0.8 date |
| SSH with verbose ouptut | ssh -vvv -p 2702 root@45.33.87.74 date 2>&1 |
| Setup ssh tunnel for your web browsing | sshuttle -r kubo@10.92.21.17 30.0.0.0/16 192.168.150.0/24 -e ... |
| SSH passwordless login | ssh-copy-id <username>@<ssh_host>, Or manually update ~/.ssh/authorized_keys |
Remove an entry from known_hosts file | ssh-keygen -f ~/.ssh/known_hosts -R github.com |
| Diff local file with remote one | diff local_file.txt <(ssh <username>@<ssh_host> 'cat remote_file.txt') |
| Diff two remote ssh files | diff <(ssh user@remote_host 'cat file1.txt') <(ssh user2@remote_host2 'cat file2.txt') |
| Upload with timestamps/permissions kept | scp -rp /tmp/abc/ ec2-user@<ssh-host>:/root/ |
| SSH agent load key | exec ssh-agent bash && ssh-add /tmp/id_rsa, ssh-add |
| SSH list all loaded key | ssh-add -l |
| SSH agent create and load key | exec ssh-agent bash && ssh-keygen, ssh-add |
| Emacs read remote file with tramp | emacs /ssh:<username>@<ssh_host>:/path/to/file |
| Generate a new key pair | ssh-keygen, ssh-keygen -C 'your_email@example.com' -t rsa |
| Generate key pair without interaction | ssh-keygen -t rsa -f /tmp/sshkey -N ' -q |
1.2 SSH Advanced
| Name | Summary |
|---|
| Add passphrase protection to ssh keyfile | ssh-keygen -p -f id_rsa |
| configure SSH to avoid trying all identity files | ssh -o IdentitiesOnly=yes -i id1.key myuser@myserver.com |
| Convert OpenSSL format to SSH-RSA format | ssh-keygen -f my_ssh.pub -i |
| Critical ssh files/folders | ~/.ssh/authorized_keys, ~/.ssh/config, ~/.ssh/known_hosts |
| SSH config file | /etc/ssh/ssh_config, /etc/ssh/sshd_config |
| SSH key file permission | chmod 600 ~/.ssh/id_rsa |
| SSH folder permission | chmod 700 ~/.ssh, chown -R $USER:$USER ~/.ssh |
| Authorizedkeys file permission | chmod 644 ~/.ssh/authorized_keys |
Mute Warning: Permanently added | ssh -o LogLevel=error |
1.3 SSH tunnel & ssh proxy
| Name | Summary |
|---|
| SSH port forward to a local port | ssh -N -i <ssh-keyfile> -f root@54.179.178.214 -L *:18085:localhost:8085 -n /bin/bash |
| Reverse port forward to remote server | ssh -R *:40099:localhost:22 root@54.179.178.214, ssh -p 40099 root@54.179.178.214 |
| Setup ssh tunnel for your web browsing | sshuttle -r kubo@10.92.21.17 30.0.0.0/16 192.168.111.0/24 192.168.150.0/24 192.167.0.0/24 |
1.4 SSH security
Brew Shop Arlington
| Name | Summary |
|---|
| Disable ssh by password | sed -i 's/PasswordAuthentication yes/PasswordAuthentication no/g' /etc/ssh/sshd_config |
| Disable root login | sed -i 's/^PermitRootLogin yes/#PermitRootLogin yes/' /etc/ssh/sshd_config |
| Enable/Disable SSH Host Key Checking | StrictHostKeyChecking yes change ~/.ssh/config |
| Protect SSH server from brute force attacks | fail2ban command line tool |
1.5 SCP
| Name | Summary |
|---|
| Download a remote folder | scp -r ec2-user@<ssh-host>:/home/letsencrypt-20180825 ./ |
| Upload a file | scp -i <ssh-keyfile> /tmp/hosts ec2-user@<ssh-host>:/root/ |
| Upload a folder | scp -r /tmp/abc/ ec2-user@<ssh-host>:/root/ |
| Upload with timestamps/permissions kept | scp -rp /tmp/abc/ ec2-user@<ssh-host>:/root/ |
| Mount remote directory as local folder | sshfs name@server:/path/remote_folder /path/local_folder |
1.6 Parse ssh log file
| Name | Command |
|---|
| Events of ssh down | grep -R 'ssh.*Received signal 15' /var/log/auth.log |
| Events of ssh up | grep -R 'sshd.*Server listening' /var/log/auth.log |
| Events of ssh failed login | grep -R 'sshd.*Failed password for invalid user' /var/log/auth.log |
| Events of ssh break-in attemp | grep -R 'sshd.*POSSIBLE BREAK-IN ATTEMPT!' /var/log/auth.log |
| Events of ssh port scap | grep -R 'sshd.*Bad protocol version identification' /var/log/auth.log |
| Events of ssh login by public key | grep -R 'sshd.*Accepted publickey for' /var/log/auth.log |
| Events of ssh login by password | grep -R 'sshd.*Accepted password for' /var/log/auth.log |
| Events of ssh logout event | grep -R 'sshd.*pam_unix(sshd:session): session closed for' /var/log/auth.log |
1.7 SSH tools
| Name | Summary |
|---|
| Export local env to Internet | ngrok.com |
| Reverse ssh proxy | sshuttle |
| SSH by auto input password | sshpass sshpass -p “$PASSWORD” ssh -o StrictHostKeyChecking=no $username@$sship= |
1.8 Scripts

- Inject local key to remote ssh server server

- Use expect to run ssh command with credential auto input

Brew Sshfs
1.9 More Resources
License: Code is licensed under MIT License.